According to a new survey from IT Brief Australia, 80% of Australian organisations surveyed were hit with ransomware in 2021, up from 45% in 2020. This presents an alarming wake-up call with the realisation of just how vulnerable systems are and the potential interruptions and losses a business may unknowingly be exposed to. Most of these attacks are of a ransomware-type, requiring payment demands to be met before the victim will experience relief. In its worldwide survey of 5,600 IT professionals in mid-sized companies, Sophos noted that the lowest average ransom payment was US $197K, while the highest average was an eye-watering US $2.04M.
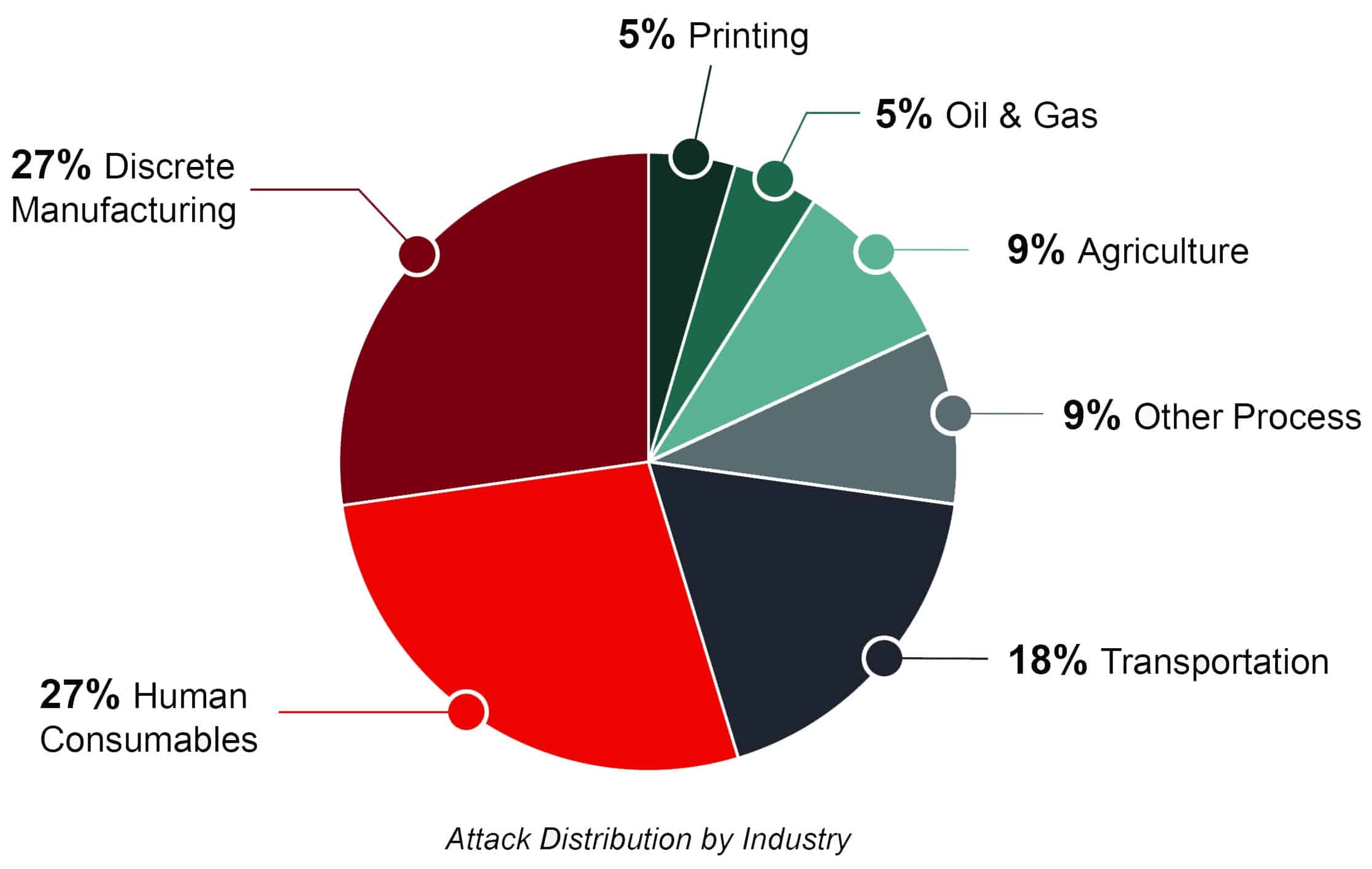
Focusing more specifically, of the 64 OT-related incidents reported in 2021, 22 were cyber-attacks with physical consequences in discrete manufacturing and process industries. These attacks represent a 144% increase over such incidents in 2020.
 Alongside the escalating payments, recent surveys show that the proportion of victims paying up also continues to increase, even when they may have other options available,” says Chester Wisniewski, a principal research scientist at Sophos. He also went on to say, “there could be several reasons for this, including incomplete backups or the desire to prevent stolen data from appearing on a public leak site”. “In the aftermath of a ransomware attack, there is often intense pressure to get back up and running as soon as possible. Restoring encrypted data using backups can be a difficult and time-consuming process, so it can be tempting to think that paying a ransom for a decryption key is a faster option. It’s also an option fraught with risk. Organisations don’t know what the attackers might have done, such as adding backdoors, copying passwords, and more. If organisations don’t thoroughly clean up the recovered data, they will end up with all that potentially toxic material in their network and potentially exposed to a repeat attack.” Despite Italy having made extortion payments illegal, it reported that 43% of those companies whose data was encrypted admitted to paying a ransom
Alongside the escalating payments, recent surveys show that the proportion of victims paying up also continues to increase, even when they may have other options available,” says Chester Wisniewski, a principal research scientist at Sophos. He also went on to say, “there could be several reasons for this, including incomplete backups or the desire to prevent stolen data from appearing on a public leak site”. “In the aftermath of a ransomware attack, there is often intense pressure to get back up and running as soon as possible. Restoring encrypted data using backups can be a difficult and time-consuming process, so it can be tempting to think that paying a ransom for a decryption key is a faster option. It’s also an option fraught with risk. Organisations don’t know what the attackers might have done, such as adding backdoors, copying passwords, and more. If organisations don’t thoroughly clean up the recovered data, they will end up with all that potentially toxic material in their network and potentially exposed to a repeat attack.” Despite Italy having made extortion payments illegal, it reported that 43% of those companies whose data was encrypted admitted to paying a ransom
But it is not just the ransom payment that is having an economic impact on businesses. Overall, the average cost to an organisation to rectify the impact of a ransomware attack in 2021 was US $1.4M, which, thankfully, is a drop from US $1.85M in 2020. On top of the cost of rectification is lost operating time. On average, organisations that suffered an attack last year took one month to recover to normal operations. Interestingly, education was the slowest to recover while manufacturing was the fastest.
What often goes unnoticed are the ‘near-misses’: incidents that had the potential for severe impact if the circumstances had been different. One example that Waterfall Security cites is the case of a water treatment plant where an attacker used an obsolete TeamViewer account to operate an HMI to increase lye concentrate in finished water, but an observant operator thwarted the attempt.
While most of the attacks reported affect IT assets, some attacks have targeted OT assets to either manipulate or impair them. Past data suggests three ways ransomware can cause physical consequences in process and discrete manufacturing industries. Ransomware actors can target;
- OT systems directly, through targeted or supply-chain attacks, resulting in impaired OT automation and operations
- IT systems indirectly, affecting OT systems when the victim enterprises shut down physical operations in an ‘abundance of caution’
- and impair IT systems that are essential to live industrial operations.
Prudent businesses must take steps to eliminate the possibility of all kinds of OT shutdowns due to ransomware attacks.
Even though there is a suggestion that we have reached a peak in the evolutionary journey of ransomware and that the greed for even higher ransom payments is meeting head-on with cyber insurers being less likely to make payouts, ransomware attacks are not as resource intensive as other attacks. Therefore, cybercriminals will continue to go after this low-hanging fruit. For this reason, Sophos recommends the following best practices to help defend against ransomware and related cyberattacks:
- Install and maintain high-quality defences across all points of the organisation’s environment. Review security controls regularly and make sure they continue to meet the organisation’s needs.
 Proactively hunt for threats to identify and stop adversaries before they can execute their attack. If there is a lack of time or skills to do this in-house, outsource to a Managed Detection and Response (MDR) specialist.
Proactively hunt for threats to identify and stop adversaries before they can execute their attack. If there is a lack of time or skills to do this in-house, outsource to a Managed Detection and Response (MDR) specialist.- Harden IT environments by searching for and closing critical security gaps: unpatched devices, unprotected machines, open Remote Desktop Protocol (RDP) ports, etc. Extended Detection and Response (XDR) solutions are ideal for this purpose.
- Prepare for the worst. Know what to do if a cyber incident occurs and keep the plan updated.
- Make backups and practice restoring from them so that the organisation can get back up and running as soon as possible, with minimum disruption.
If you have not taken steps to protect yourself against the chance of a cyber attack, then now is the time to be proactive about it. You may like to consider Nozomi or Octoplant as possible solutions to help you secure your IT & OT assets.
Those who want to read the reports that some of this content is based on can access the following documents as linked:
SOPHOS – The State of Ransomware 2022
OT Security Incidents: 2021 Trends and Analysis