Have you ever wondered what the best way would be to connect your systems to the plant?
We have been asked this many times, and the reasons why we are asked varies a lot. There is no simple answer. The solution will depend on many different factors and includes:
- · Open networks
- · Protected networks (e.g. a DMZ)
- · Edge devices and data pipes (Gateways)
- · Independent Sensors
- · Secure and insecure interfaces
- · Mixed topologies
The most significant factor affecting our answer is the existing standards and equipment. Is the equipment relay controlled? Are there ethernet connected PLCs? Is there a SCADA in place? Other factors to consider are the likelihood of hacking or other security threats, as well as the financial, logistical or other consequences of having downtime in the plant? Opening your system increases your vulnerability. Most people don’t think about the potential cost or risk of their data being stolen; they feel that the cost of mitigating this risk is unwarranted and expensive. Mescon would argue that this is dangerous with the rise of cyberattacks. Data is extremely valuable, which makes the cost of securing that data a justifiable expense. Multiple levels of security, including isolation, gateways, DMZs, monitoring, in conjunction with regular reviews and audits, should be considered as standard.
We will now explore the benefits and risks of the connectivity methods mentioned above.
Open Network
This is the most common solution because it is quick and easy. All devices are plugged into one network. These networks often grow slowly and are not designed with consideration of all the equipment that will be attached to the network.
The Open Network creates a system that is extremely vulnerable to inside and outside disturbances. It opens control systems to personnel that do not understand the consequences and risks of production systems. We have seen production stop due to front office PC activity. A level of isolation is typically necessary.
Protected network
The protected network, e.g. DMZ, is similar to an open network but slightly more protected. The theory is that only authorised traffic can get to authorised equipment.
The issue is that over time, the rules are relaxed, and the system becomes open with many well-known holes, especially if the IT help desk has permission to modify router and firewall settings.
Remote control software (e.g. VNC or Dameware) is the most common hole seen. These tools, which may only have a single password, allow any user that has access to the network to take control of remote PCs, including terminals that control equipment such as SCADA terminals. They allow the users to do whatever they want as if they were physically at the terminal, except hitting the screen with a hammer!
Edge Devices
A common remote access solution for engineers is to include a device that has independent access to both plant and corporate networks. With an Edge Device, e.g. Gateway, data comes in from one network and goes out the other network in a controlled manner.
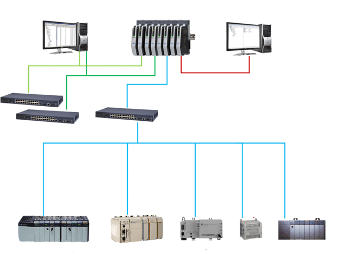
An example of an edge device is one that has two independent Ethernet ports. This may be an OPC server with dual network cards, a PLC or an industrial gateway. The control network is connected to one port and the corporate network to the other port. The device collects and re-distributes the data.
Independent Sensors
Typically found in IoT devices, the concept is that the device is not connected to or a part of the control system. While an independent sensor can detect a change in state and communicate the change across a network, it cannot communicate with the control system.
It is the separation from other networks that creates the secure system. For example, if you want to know the temperature of an oven outside of the control system, then you measure it independently.
 The concepts of “lick and stick” sensors or battery-powered wireless devices are common. Their advantage is in their independence from production systems; they can only influence production through justified procedural changes. However, they are typically inferior sensors in robustness and accuracy.
The concepts of “lick and stick” sensors or battery-powered wireless devices are common. Their advantage is in their independence from production systems; they can only influence production through justified procedural changes. However, they are typically inferior sensors in robustness and accuracy.
Secure and Insecure Interfaces
Many devices can allow external departments access to a control network—for example, VLANs, gateways, protocol diverters, routers, firewalls. Although initially set up well, such devices become less secure over time as changes are made that bypass the device. Often these changes (e.g. cabling being installed) are made without knowledge of the initial set-up criteria.
One device that we love the concept of is a uni-directional gateway. This allows network traffic to only travel from the control network to the enterprise network. Some may have a bypass switch that will allow access the other way for a specified time to enable remote support.
The most significant security risk to any system is not the planned security of the system but the unplanned. To overcome this, you should use a network monitoring solution that takes a signature of the network traffic and will deny unusual traffic. Software like Videc’s solution IRMA is much more suitable for control networks than traditional IT department monitoring software that often only picks up outages.
Mixed Topology
The best solution is a mixture of all of the above solutions. Different scenarios and needs require different solutions. Any solution needs to consider three things: existing control and enterprise networks, the risk of data loss, and price. You need to use the right architecture and concept to suit the needs of the environment.
If you need assistance, then reach out to experts in the relevant field.